Question
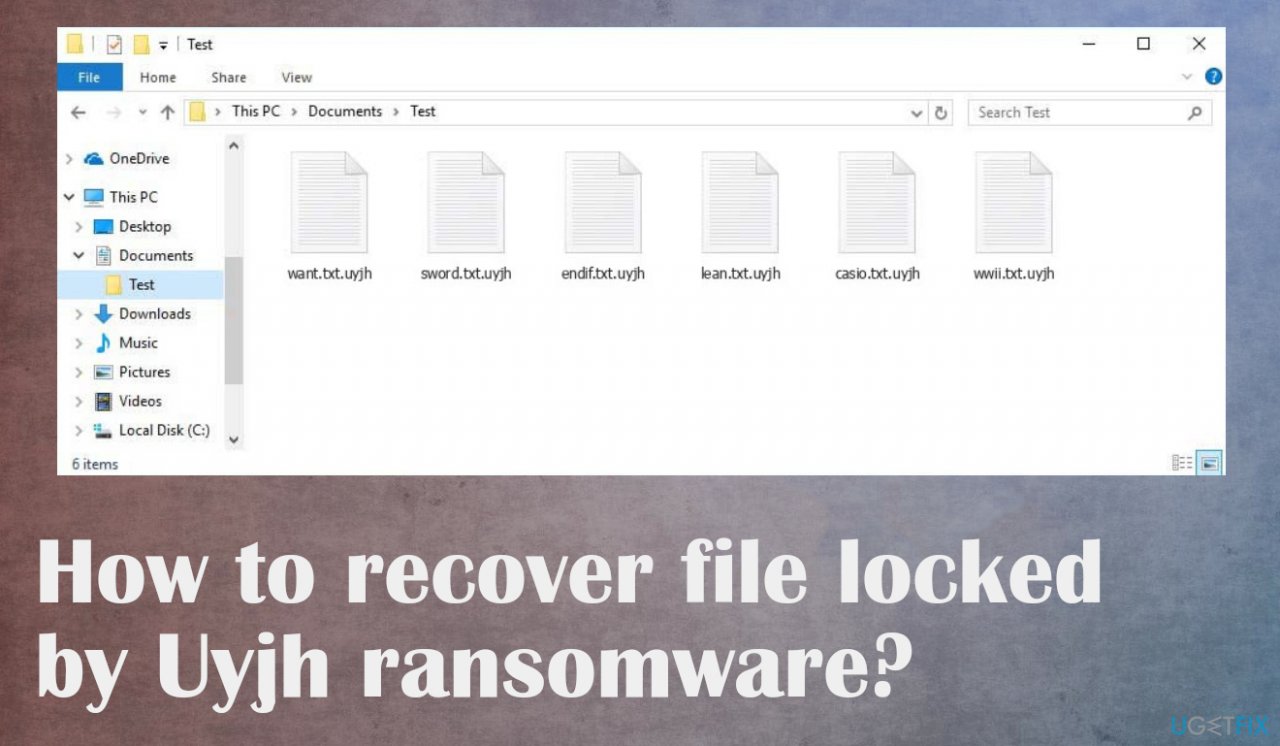
Issue: How to recover file locked by Uyjh ransomware?
I downloaded some programs from torrents and I guess now I have this ransomware on the machine. I know it is my fault, but I need to get my files back. Backups are not up to date and I need my university work to get recovered. The extension is .uyjh. I cannot find decryption options online. I need help! Can you offer any solutions?
Solved Answer
The worst thing about these threats is the file-locking process because the infection starts silently and once data is encrypted, the ransom gets demanded. Uyjh ransomware demands money via text file _readme.txt and scares people with claims about the option of decrypting files.
The amount is $980 in the form of Bitcoin, but criminals even offer a 50% discount to encourage people to pay the sum. This is the worst solution because criminals cannot provide solutions and the decryption tool in exchange for the payment. The options here are limited, unfortunately.
It is due to the changes that Djvu ransomware creators have made in recent years. It is more advanced and improved, so users have no option but to pay the ransom to restore their data.[1] The ransomware creates various issues and the malware is controlled by the criminals, so once those files get locked, note that the machine has been already compromised further than file-locking.
More on the ransomware infection
The Uyjh file virus is one of the more recent ransomware viruses to make its way online. This type uses game or software cracks, pirated packages for NBA games among other things in order to deliver threats.[2] Creators release new versions very often, so there are a lot of versions out at the same time.
It's no surprise that the ransomware virus creators are relying on fear tactics and false claims about possible decryption methods. They offer 50% off if paid before 72 hours, but their only goal is to get money from you as quickly as possible with dangerous offers. You should also avoid connecting with the criminals via emails like [email protected] or [email protected]. There are alternate options for threat removal and file repair. Focus on those.
1. Remove the active virus before anything else
Threat actors use various methods to infiltrate and often there are various trojans, malware involved in the distribution. Even when you get those files locked after the pirating software installation or due to the malspam emails with malicious attachments[3] and viruses, you can receive additional threats too.
Anti-malware tools are needed here because the program can detect all possibly malicious programs and files running on the system. Threats can affect the performance and ransomware persistence, so run the proper antivirus tool and remove Uyjh file virus from the machine.
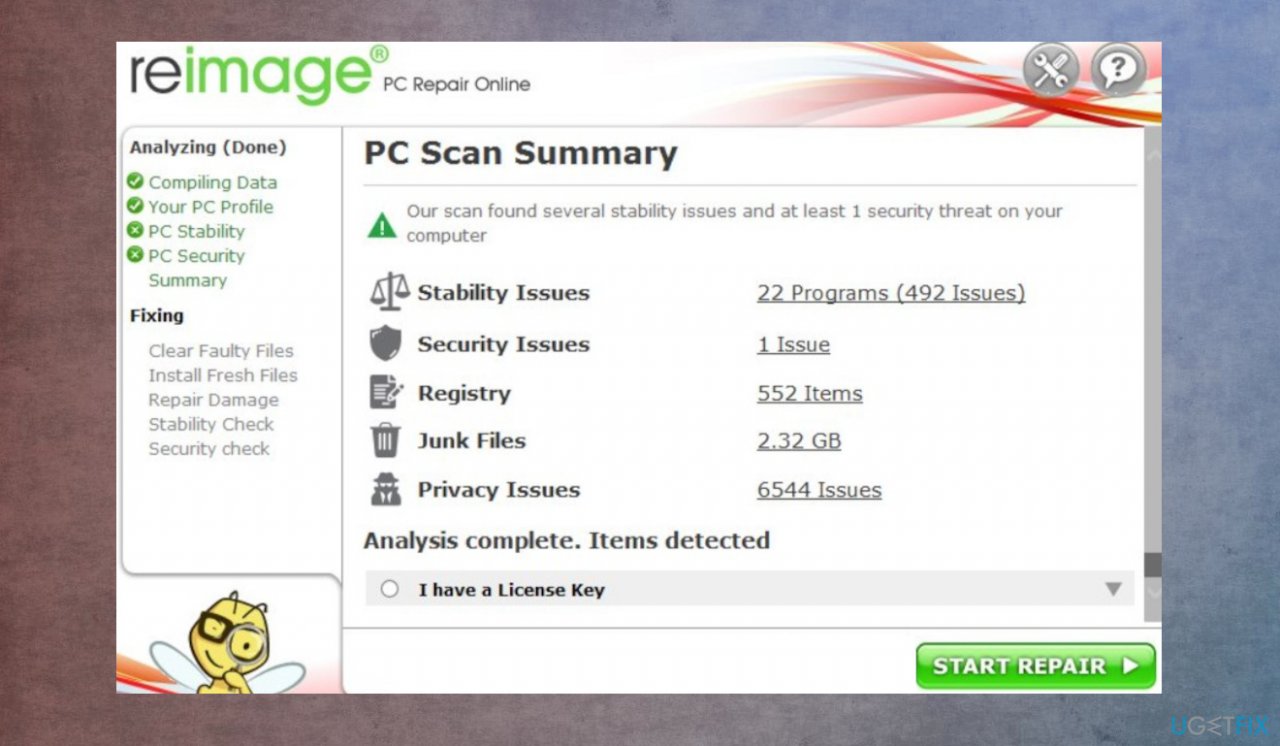
2. Repair corrupted or altered system files
Various system processes are controlled by the files in the system folder. There are additional issues that the threat creates and users cannot notice. The DLL files and Windows operation system data can get corrupted by the ransomware that runs on the machine. It affects various processes needed for ransomware removal and file recovery.
- Install the PC optimization app like FortectMac Washing Machine X9.
- Run the full system scan and wait for the complete analysis.
- Follow the on-screen steps.
- Allow the machine to get checked.
- Check the Summary.

- You can fix issues manually from the list.
- Purchasing a licensed version can help repair serious issues.
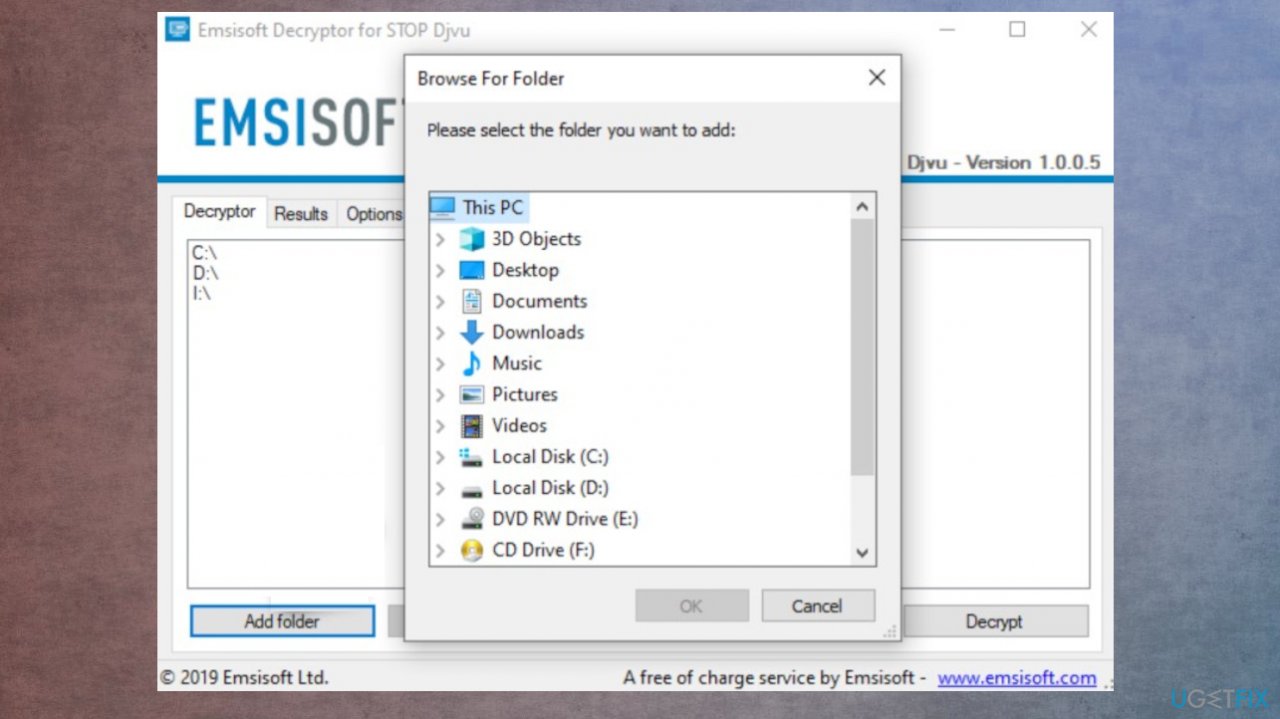
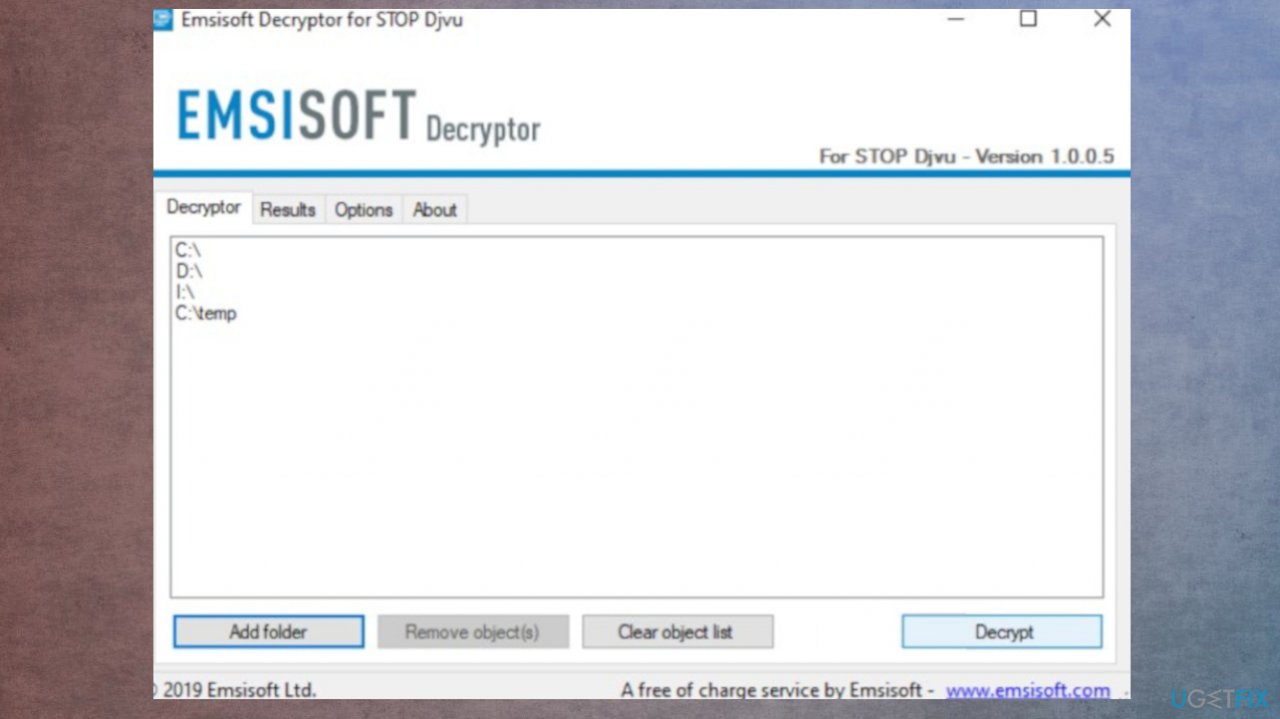
3. Check if the decryption is possible
Threat family is known for a while, but the decryption tools take a lot of time to develop, especially when these ransomware creators make advanced changes to their malware. Offline IDs that were used by one version to all devices were helpful in the past, but this option is no longer used. Online Keys are primarily used by the Uyjh ransomware, so options here are limited, but you still should check the opportunity.
- Download the app on official Emsisoft website.
- Once decrypt_STOPDjvu.exe shows up – click it.
- Follow the steps on the screen.

- The tool should locate the affected folders.
- You can also do it by pressing Add folder at the bottom.
- Press Decrypt.

- Results determine decryption options.
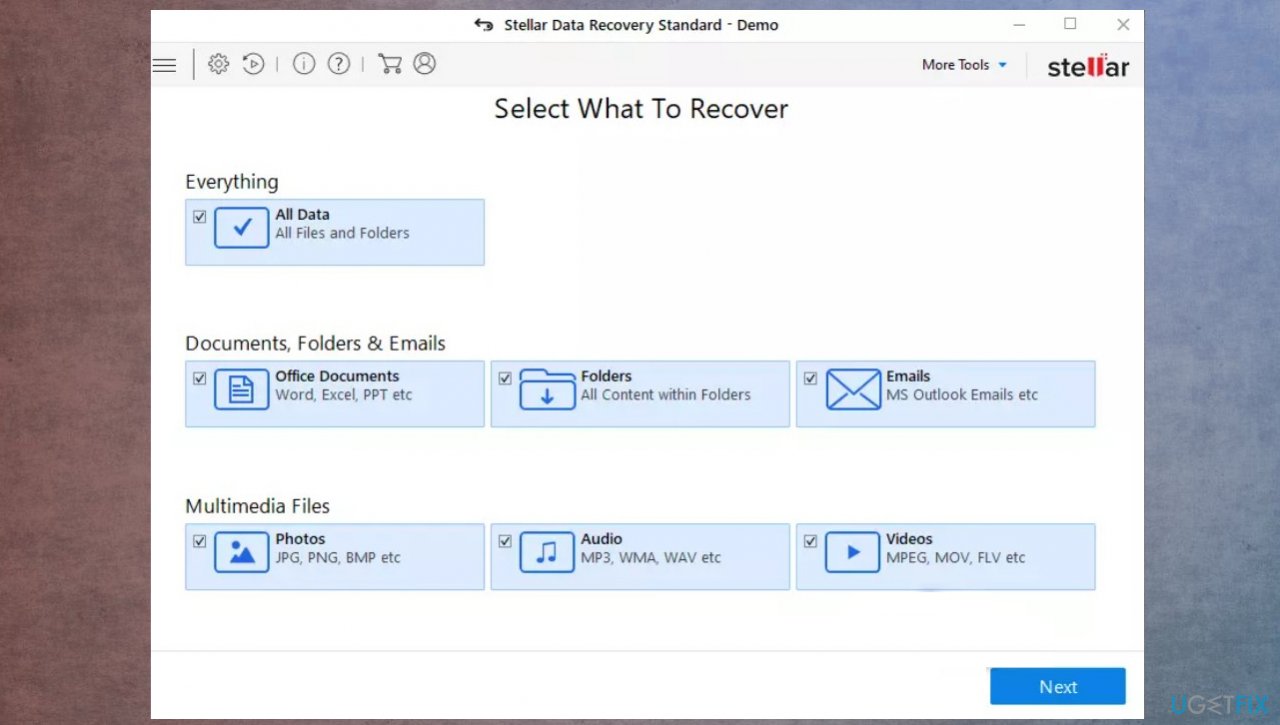
4. Try to use the data recovery tool
- We can recommend Data Recovery Pro.
- Follow installations.
- Once that is finished, use the application.

- Select Everything or pick individual folders to recover.
- Press Next.
- Enable Deep scan at the bottom.
- Pick which Disk you want to be scanned.
- Scan.
- Hit Recover to restore files.
Recover files and other system components automatically
To recover your files and other system components, you can use free guides by ugetfix.com experts. However, if you feel that you are not experienced enough to implement the whole recovery process yourself, we recommend using recovery solutions listed below. We have tested each of these programs and their effectiveness for you, so all you need to do is to let these tools do all the work.
Protect your online privacy with a VPN client
A VPN is crucial when it comes to user privacy. Online trackers such as cookies can not only be used by social media platforms and other websites but also your Internet Service Provider and the government. Even if you apply the most secure settings via your web browser, you can still be tracked via apps that are connected to the internet. Besides, privacy-focused browsers like Tor is are not an optimal choice due to diminished connection speeds. The best solution for your ultimate privacy is Private Internet Access – be anonymous and secure online.
Data recovery tools can prevent permanent file loss
Data recovery software is one of the options that could help you recover your files. Once you delete a file, it does not vanish into thin air – it remains on your system as long as no new data is written on top of it. Data Recovery Pro is recovery software that searchers for working copies of deleted files within your hard drive. By using the tool, you can prevent loss of valuable documents, school work, personal pictures, and other crucial files.
- ^ Norman Guadagno. The evolution of a cybercrime: a timeline of ransomware advances. Comcast. Business cybersecurity.
- ^ Sergiu Gatlan. Malware hidden in game cheats and mods used to target gamers. Bleepingcomputer. IT and cybersecurity news.
- ^ Mac virus. Wikipedia. The free encyclopedia.