Question
Issue: How to recover files encrypted by Nesa ransomware?
Hello, I am infected with a virus. My pictures, videos, documents, and other files are all unusable. I cannot open them in any way! The icons have changed to blank ones, and each file has .nesa instead of .jpg, .pdf, and others. How do I recover my files back? Please help me!
Solved Answer
Nesa ransomware is the newest version of the STOP/Djvu ransomware family. Since its release in December 2017, the variants of this malware strain have been released over 150 times. However, the frequency version releases are not the only feature that makes this family so devastating – cybercriminals behind it are working hard on implementing new features and expanding operations by employing sophisticated distribution techniques.
Just as many previous STOP/Djvu versions, Nesa ransomware can be distributed in an array of various methods, including exploit kits, adware bundles,[1] unprotected Remote Desktop[2] connections, fake updates, hacked sites, drive-by downloads, spam emails, etc. Using several distribution vectors increases the chance of more users being infected with Nesa virus, consequently increasing the rate at which criminals can get paid.
Nesa ransomware is crypto-malware, so its main goal is to lock all pictures, documents, PDF, and other personal files with the help of an asymmetric encryption algorithm. This way, the malware prevents victims from accessing all the data located on the computer, along with any connected storages or networks.
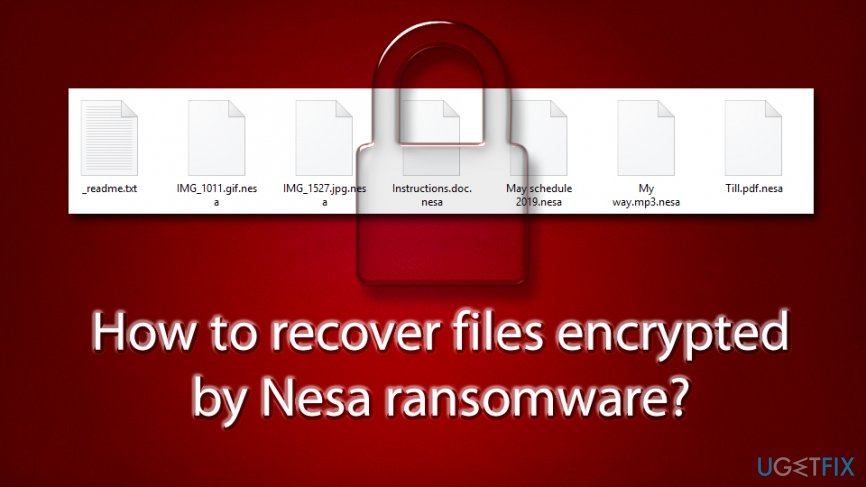
While one might this that files have been corrupted, it is not the case – .nesa file extension serves like a lock, which needs a key to be opened. The key is in the possession of malicious actors behind the virus, and it is kept on a remote Command & Control[3] server.
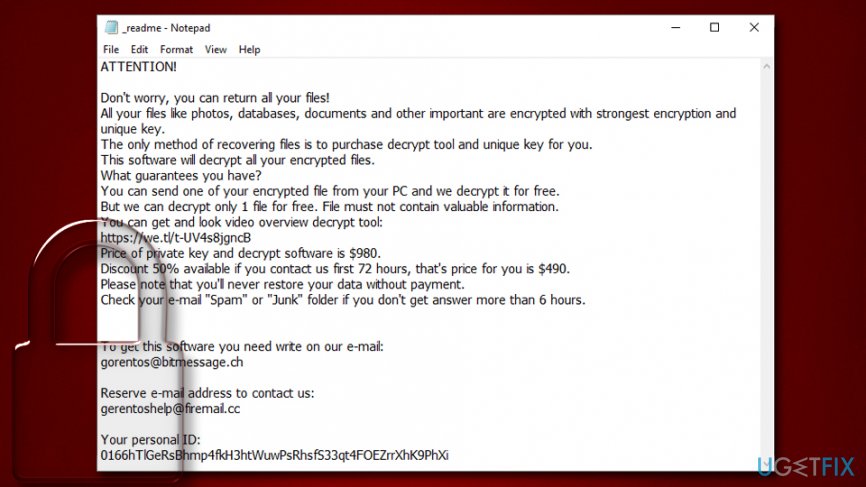
Users are typically informed via the ransom note _readme.txt about the situation, and explain that, if they want to retrieve the decryption tool, they need to pay $980 worth of Bitcoin as a ransom, although hackers claim that users are eligible for 50% discount if they contact the crooks via [email protected] or [email protected] emails and agree to transfer the money.
However, security experts advise not paying the ransom, as hackers might never send the required Nesa decryptor, even after the payment is made. Besides, rewarding cybercriminals for their malicious deeds would only encourage them to produce a new and improved version of the virus. In other words, by paying them, users are fueling the need for creating more malware and infecting more victims, which is why ransomware is one of the leading malware types in the wild.
Instead, you should remove Nesa ransomware with the help of security software like FortectMac Washing Machine X9 (be aware that, due to ever-changing and improved version variants, the removal might require a scan with several anti-malware tools) and then use alternative methods to recover files encrypted by Nesa ransomware.
How to decrypt .nesa files?
First spotted by security research Michael Gillespie,[4] Nesa ransomware showed up in late September 2019. It also belongs to the new wave of STOP versions that use an improved way of encrypting files. In addition, the malware also drops a new module which is capable of harvesting personal user information, consequently leading to sensitive data and money loss.
Another feature of Nesa virus is its ability to modify Windows hosts file. This change ensures that users are unable to seek help at security-focused websites. However, all these changes are reversible with the help of Nesa ransomware elimination – we explain how to do that below.
What is not reversible, however, are the files. Even after the termination of the infections, victims will not be able to view their files, and they will remain locked. This feature, in particular, is what makes ransomware so devastating – it can result in permanent data loss.
As we previously stated, paying the ransom is quire risky, and most of the experts advise not to do it. While retrieving .nesa locked files in other ways might not be possible, there are still chances that they will help, or, at least, partially. In the next section, we provide detailed instructions on how to remove Nesa ransomware and how to attempt file recovery by using alternative methods.
Step 1. Remove Nesa ransomware from your computer
We highly discourage you from trying to eliminate the ransomware manually, as the threat makes hundreds of changes to the computer, and reverting those would require professional IT knowledge. Instead, you should employ a powerful anti-malware software and perform a full system scan with it – it should delete the infection automatically.
However, Nesa ransomware might tamper with your anti-malware tool. In such a case, you should access Safe Mode with Networking and perform the scan from there:
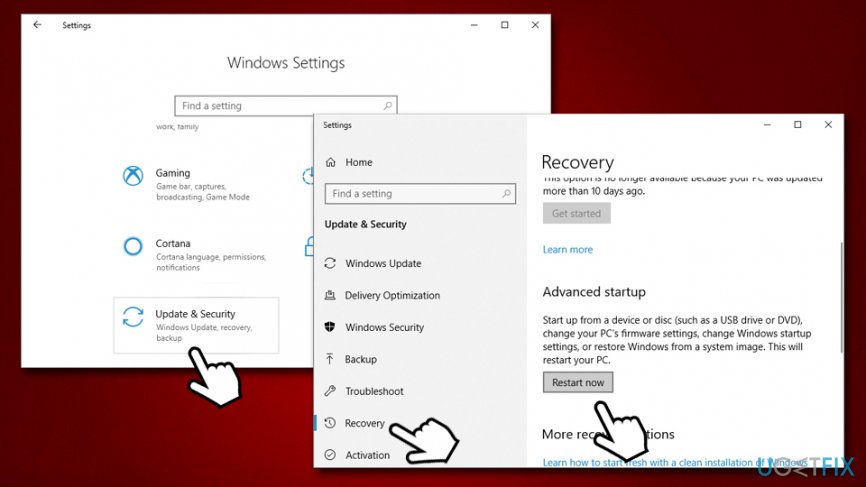
- Right-click on Start button and select Settings
- Go to Update & Security section and pick Recovery
- Find Advanced startup and click on Restart now (note: this will immediately restart your computer)

- Then, select the following path: Troubleshoot > Advanced options > Startup Settings and click Restart
- After the reboot, press F5 or 5 to to reach Safe Mode with Networking
Perform a full system scan with anti-malware software. After than, you should go to the following path:
C:\\Windows\\System32\\drivers\\etc
Once there, find a file called hosts. Right-click on it and press Delete. Empty your Recycle Bin afterward. 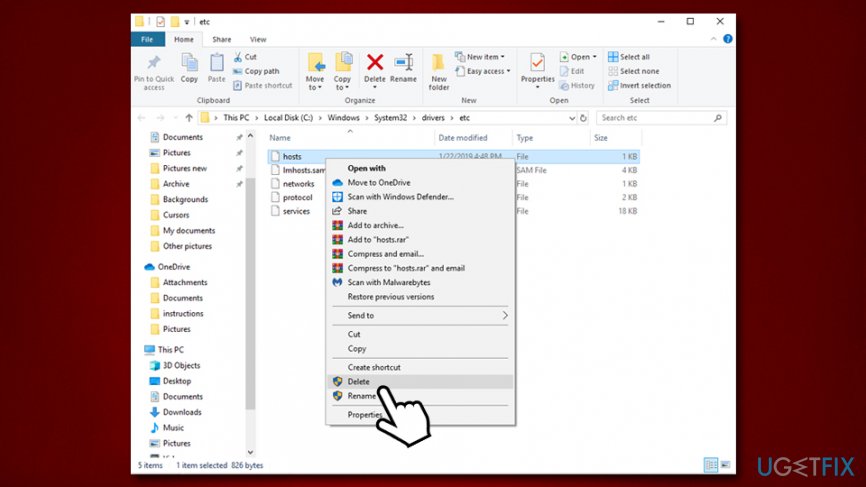
Step 2. Try using Data Recovery Pro for .nesa locked files
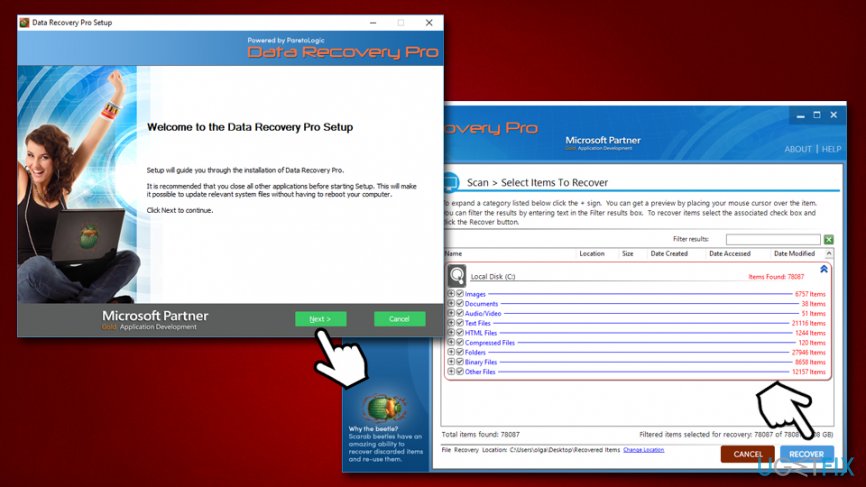
Depending on how much you used your computer after Nesa infection, Data Recovery Pro may or may not help you with (partial) recovery. However, you should try it, as it is one of the best recovery tools on the market today:
- Start with downloading Data Recovery Pro [link]
- Use on-screen instructions to install the application. Once done, double-click on Data Recovery Pro shortcut on your desktop to open it
- Select Full Scan option and click on Start Scan (you can also search for individual files based on keywords)
- After the scan finishes, see if any of your files got recovered. If so, click on Recover to retrieve them

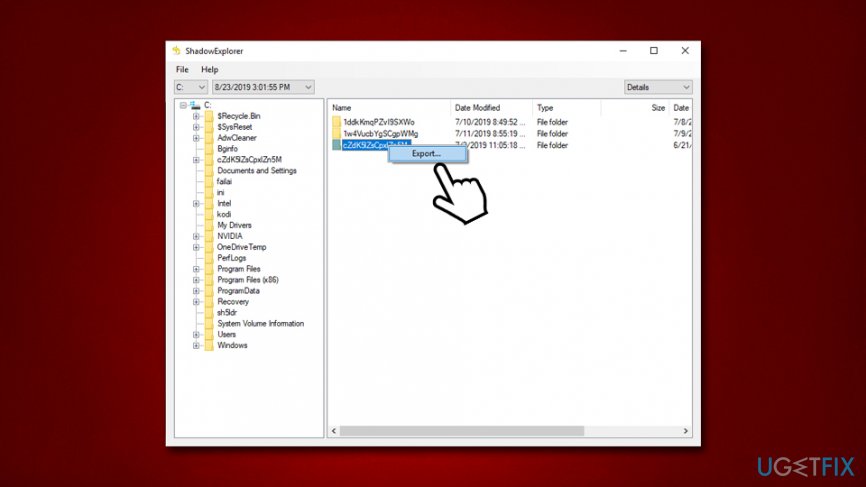
Step 3. ShadowExplorer could potentially restore all your data
Almost all ransomware viruses are programmed to delete Shadow Volume Copies – and automatic backup system used by Windows. Nevertheless, this function might fail or be skipped. Tools like ShadowExplorer are ideal for such scenarios, and should most likely be able to recover .Nesa files.
- Install ShadowExplorer [link]
- pick the drive and the the folder you want to recover
- Right-click and select Export

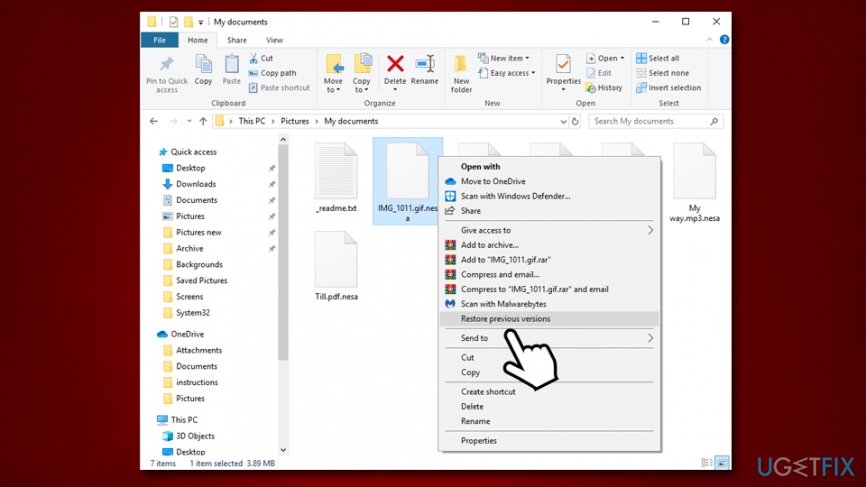
Step 4. Try a built-in Previous Versions Feature
Windows Previous Versions feature is easy to use and does not require any external programs. However, the downfall of it is that it only works if System Restore was enabled prior to the ransomware attack and only one time at the time can be recovered. Nevertheless, you should try this method as well:
- Go to the folder where the locked files are located
- Right-click on the file and choose Restore previous versions
- Select the version you want to restore it to and pick Restore

Optional: Try Dr.Web Rescue pack service
Dr.Web is one of the anti-virus makers that was deeply involved in SROP/Djvu ransomware since the very beginning – the researchers developed working decryption for .DATAWAIT, .DATASTOP and similar versions of the virus. However, as expected, hackers were quick to develop new variants for which the tool did not work anymore.
Nevertheless, Dr.Web offered help to victims in return for a certain amount of payment. Without a doubt, the firm is asking much less than ransomware developers (Rescue pack costs €150), and they are no criminals. So if you opt for paying, rather choose Dr.Web instead of crooks. Note: It is possible that not all files can be decrypted by Dr.Web, please contact them to find out more.
You can find all the details here and also apply for the service. Note that, if you had Dr.Web software installed during the infection of Nesa ransomware, the service is completely free.
No recovery methods helped? Don't panic…
Nesa ransomware is a quite devastating infection, as it might result in permanent loss of files that not only consists of hours of work but also has sentimental value. Therefore, some users might see no other option but pay cybercriminals to return their precious files. Before you do that, however, you should keep in mind that security researchers are constantly working on alternative tools that might help users in some cases. You can try using this tool, although .nesa version to it has not been added yet, although it will likely change in the future.
Finally, if you are out of options, and you are desperate to retrieve your files, go ahead and pay cybercriminals. However, do it at your own risk, as there is no guarantee that you get the Nesa ransomware decryptor from malware authors.
Recover files and other system components automatically
To recover your files and other system components, you can use free guides by ugetfix.com experts. However, if you feel that you are not experienced enough to implement the whole recovery process yourself, we recommend using recovery solutions listed below. We have tested each of these programs and their effectiveness for you, so all you need to do is to let these tools do all the work.
Prevent websites, ISP, and other parties from tracking you
To stay completely anonymous and prevent the ISP and the government from spying on you, you should employ Private Internet Access VPN. It will allow you to connect to the internet while being completely anonymous by encrypting all information, prevent trackers, ads, as well as malicious content. Most importantly, you will stop the illegal surveillance activities that NSA and other governmental institutions are performing behind your back.
Recover your lost files quickly
Unforeseen circumstances can happen at any time while using the computer: it can turn off due to a power cut, a Blue Screen of Death (BSoD) can occur, or random Windows updates can the machine when you went away for a few minutes. As a result, your schoolwork, important documents, and other data might be lost. To recover lost files, you can use Data Recovery Pro – it searches through copies of files that are still available on your hard drive and retrieves them quickly.
- ^ Bradley Barth. Downloads of cracked software distribute ransomware via adware bundles. SC Magazine. IT security news.
- ^ Jakub Křoustek. Ransomware attacks via RDP choke SMBs. Avast. Security blog.
- ^ Kashinath T. Command And Control Servers : Things You Should Know. SecPot. Security solutions.
- ^ Michael Gillespie. #STOP #Djvu #Ransomware w/ extension ".nesa" . Twitter. Social network.