Question
Issue: How to recover files locked with .udla extension?
Hello. I am devastated. My files that I need for university work got encrypted and locked. Now documents, images, even audio files are all marked with .udla extension. So this is ransomware? I think I caught that when trying to get the Adobe program from torrents. Bad on my end. However, can I do anything about it?
Solved Answer
Ransomware is a cyber threat that focuses on army-grade encryption[1] and direct money extortion procedures. The latter is possible because of the file-locking because people get scared into paying the demanded sum via ransom note _readme.txt that is appearing on the machine once files get marked with .udla extension.
Cybercriminals are targeting people by falsely claiming that their data can be unlocked, so they contact hackers and pay large sums. The exchange rarely happens, so people are left without money and with damaged data. Sometimes victims will just receive another message demanding more payments instead of getting access to decrypted files or decryption tools.
The Udla file virus is a version of Djvu ransomware that uses NBA game cracks, software licenses, or pirating packages to deliver these threats with the help of malicious files with macro viruses, for example. Creators release new versions with minimal alterations in order to make them unique from other types while staying under the radar.
It happens at least weekly, and all the newer versions are no longer decryptable. At least easily or quickly. You need to react to the infection right away, so the virus is stopped, and then files can be recovered using alternate options. Paying is never recommended because ransomware creators rely on extortion all the time.[2]
1. Terminate the virus
The best way to get rid of this pesky virus is by using an anti-virus tool. The one thing you need in order for it to work properly though, and what will help keep your system safe from any additional malware or cyber threats altogether. If there's anything additional installed beside the Udla ransomware, tools like this help to find them.
This is a very serious threat that you should never ignore. The file virus can cause more problems and harm your machine if left unchecked by an anti-malware tool or security program. These encoded files themselves are not malicious, but there are data placed on the machine, like EXE or DLL pieces that have been known to carry additional malware.
Detection rates[3] determine how well these programs are able to remove active viruses from the system once they've been detected. This is not the same as file recovery or decryption, do not forget about that.
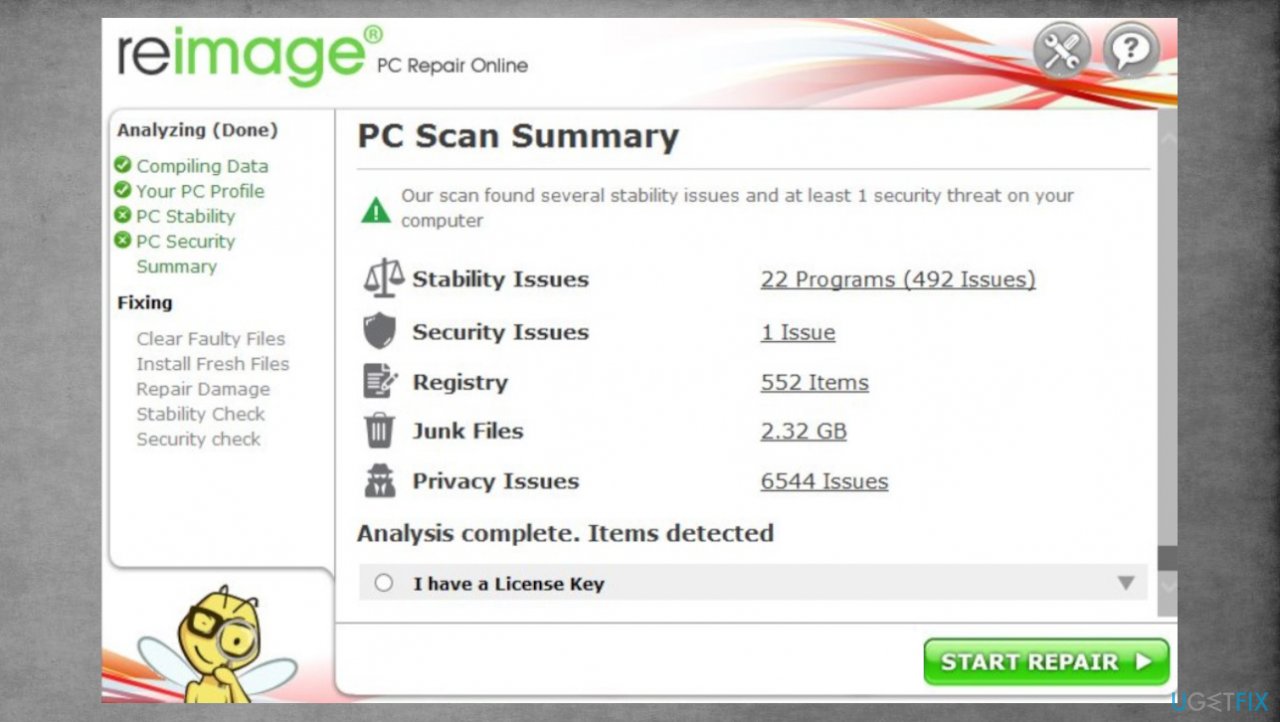
2. Repair altered or corrupted system files
Data in various system folders can be damaged and this is the issue with virus leftovers and damage. You need to take care fo this before the file recovery can be introduced.
- Get a program like FortectMac Washing Machine X9.
- Download the app from a trustworthy source.
- Launch installation procedure.
- Once the program is running, start the system analysis.
- Check the results in the Summary.

- Fix problems that are detected.
- We recommend you purchase the license and fix them automatically.
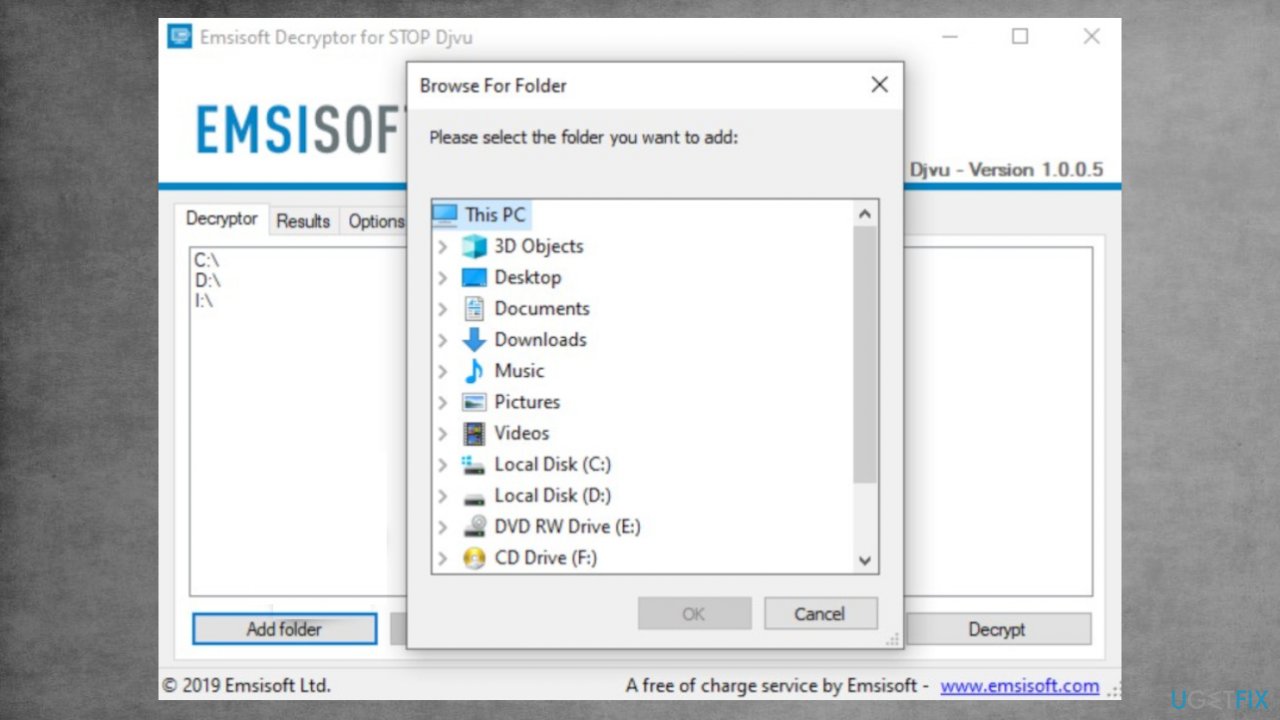
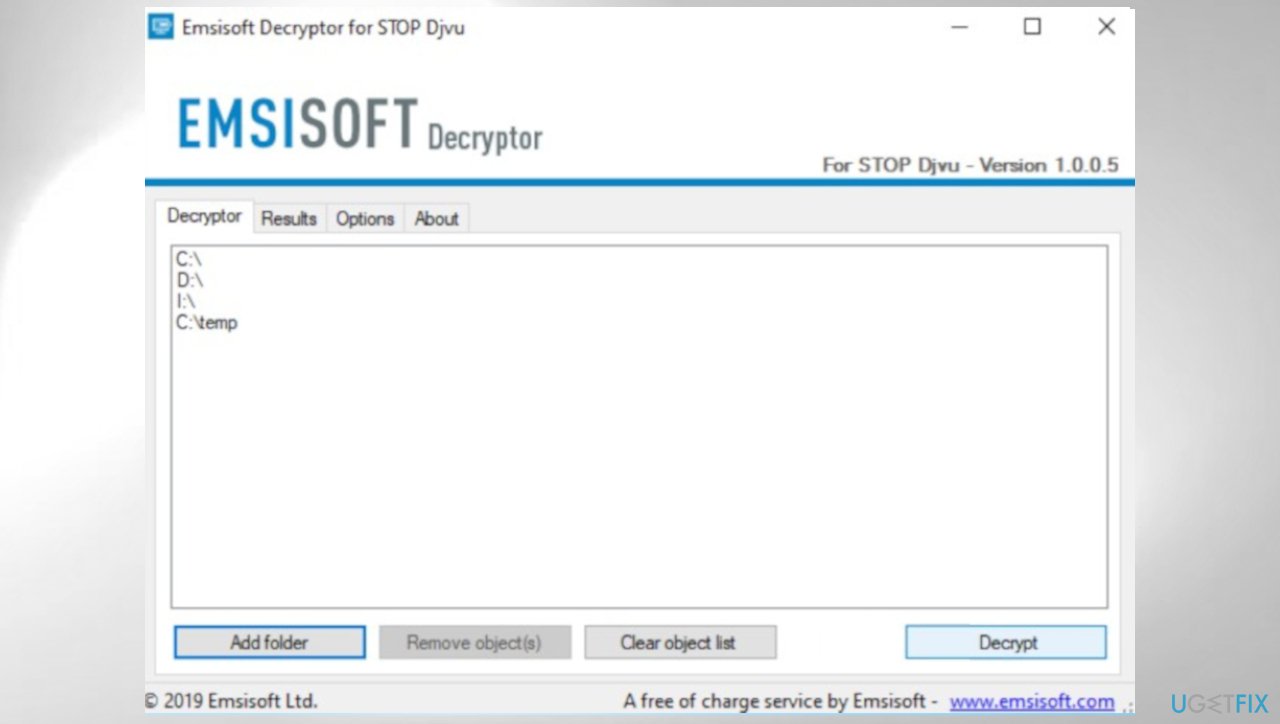
3. Check if the decryption tool can work
The offline key forming feature of this program was previously very helpful because it gave access to all victims of some of the versions. The tools helped victims to recover their data. However, now that each device has its own unique key made during the infection process the option is not available. Online keys are mainly used nowadays, but sometimes the connection might fail, so try to check if the tool can help you.
- Download the app on official Emsisoft website.
- Once decrypt_STOPDjvu.exe shows up – click it.
- Follow instructions on the screen.
- The tool should automatically locate the affected folders.
- You can also do it by pressing Add folder at the bottom.

- Press Decrypt.
- There are particular results that can occur. Those determine if the decryption option is possible for your files or not.

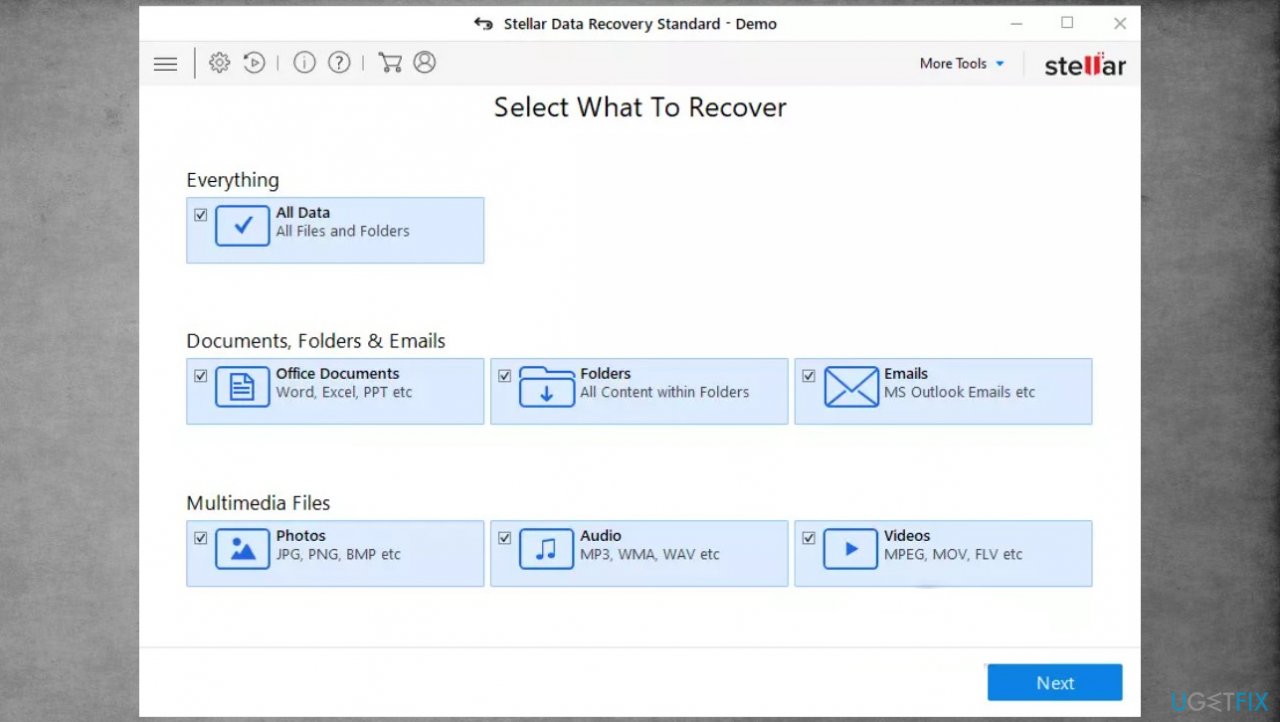
4. Recover data using the particular application
- Get a program like Data Recovery Pro that is designed to restore files.
- Install it fully n the machine.
- Follow the instructions.
- Select Everything or pick individual folders for recovery.
- Press Next.

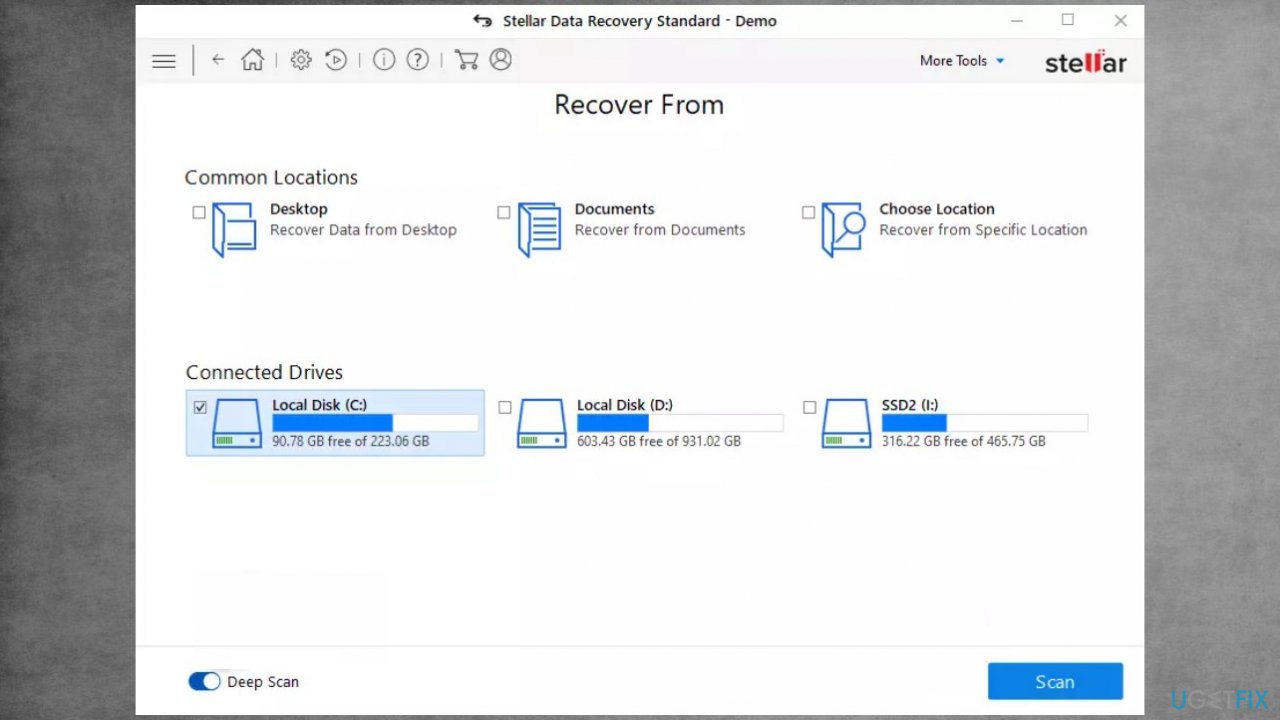
- Enable Deep scan and pick which Disk you want to scan.
- Press Scan and wait for the process to end.

- You can now pick which folders/files to recover.
- Press Recover to repair your files.
Recover files and other system components automatically
To recover your files and other system components, you can use free guides by ugetfix.com experts. However, if you feel that you are not experienced enough to implement the whole recovery process yourself, we recommend using recovery solutions listed below. We have tested each of these programs and their effectiveness for you, so all you need to do is to let these tools do all the work.
Protect your online privacy with a VPN client
A VPN is crucial when it comes to user privacy. Online trackers such as cookies can not only be used by social media platforms and other websites but also your Internet Service Provider and the government. Even if you apply the most secure settings via your web browser, you can still be tracked via apps that are connected to the internet. Besides, privacy-focused browsers like Tor is are not an optimal choice due to diminished connection speeds. The best solution for your ultimate privacy is Private Internet Access – be anonymous and secure online.
Data recovery tools can prevent permanent file loss
Data recovery software is one of the options that could help you recover your files. Once you delete a file, it does not vanish into thin air – it remains on your system as long as no new data is written on top of it. Data Recovery Pro is recovery software that searchers for working copies of deleted files within your hard drive. By using the tool, you can prevent loss of valuable documents, school work, personal pictures, and other crucial files.
- ^ Encryption. Wikipedia. The free encyclopedia.
- ^ Ransomware Hackers Demand $70 Million In Bitcoin. Forbes. Media company.
- ^ Virus sample detection. VirusTotal. Online malware scanner.