Question
Issue: How to recover files encrypted by Ryuk ransomware?
Hello, I need help urgently! I recently opened an email attachment which I now understand was fake. It was presented as an Invoice, so I thought it is something important. Soon after I opened it, I saw a text file RyukReadMe.txt file generated on my desktop. When I opened it I realized that all my files are locked now. I do not have much experience with cyber infections, and I do not want to pay the ransom. Is that the only choice?! Please help me, I have several hundred photos that are important to me!
Solved Answer
Ryuk ransomware is a relatively new cyberthreat that recently hit the headlines of various security networks, as it managed to extort nearly US$640,000 from victims.[1] While it mainly targets organizations, it is well known that the malware also attacks regular users with somewhat decreased ransom size.
It is highly likely that most users get infected when they open suspicious attachments in the spam email or click on on a disguised hyperlink. That is why it is vital to make sure that the attachment or the link is legitimate before even trying to open it. If victims are more careful online, they would not have to worry how to recover files encrypted by Ryuk ransomware in the first place.
However, many users neglect security procedures, whether it is due to lack of the information or laziness. While general users are most likely to be infected via phishing[2] emails, organizations are highly likely to be affected using brute force[3] targeted attacks.
Before the malware starts to encrypt data, it shuts down several services and processes that are running on Windows machines. Additionally, it stops several anti-malware programs from the operation and attempts to delete Shadow Volume Copies.[4] Then Ryuk ransomware scans the device in order to look for files to encode. It uses a combination RSA-4096 and AES-256 encryption algorithms to lock up data and then drops ransom note RyukReadMe.txt and UNIQUE_ID_DO_NOT_REMOVE.txt, depending if the infected target is an organization or a regular user. Hackers demand a massive amount of 15 – 50 BTC ($100,428 – $334,763) for file release.
Researchers speculate that the malware was most likely created by the infamous Lazarus hacker group that was responsible for Sony hack back in 2014, as well as the devastating WannaCry ransomware attacks. Thus, the virus is operated by high-profile hackers who are willing to extort thousands of dollars. Nevertheless, users should not contact criminals, as there is no guarantee that they will receive the decryptor. More importantly, victims who pay only fund hackers' illegal activities.
The official decryptor has not been released yet, although there are several methods you can use to recover files encrypted by Ryuk ransomware. We prepared a detailed guide below on what you should be doing next, so read it carefully.
Remove Ryuk ransomware using reputable security software
Users who got their machines infected with should first remove Ryuk ransomware and only then attempt the file recovery. Beware that manual elimination is not a smart idea, as the system might be damaged even further (tampering with system files while not being an IT expert is never recommended). Therefore, use reputable security software instead. After Ryuk ransomware removal is complete, use FortectMac Washing Machine X9 to clean up all the mess that the virus left on your computer.
Recover your files encrypted by Ryuk ransomware using data backups
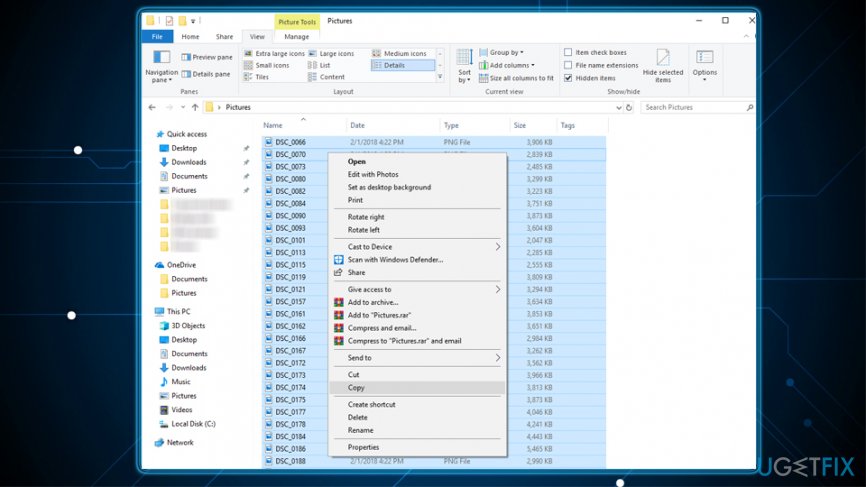
Using backups is the only guaranteed way that can get your files back. Therefore, it is vital to continually keep backups on a remote drive – such as USB stick or external HDD. Alternatively, the encoded data can be recovered from a virtual disk, such as Google Drive, OneDrive, Dropbox and similar. To restore your files using the external drive, use these instructions:
- Plug in a storage device to your computer only AFTER you removed Ryuk virus
- After the PC detects the external drive, and open the folder that contains your files
- Select all the files using Ctrl + A and press Ctrl + C after
- Go to the desired destination on your device and press Ctrl + V
Recover your files using Data Recovery Pro
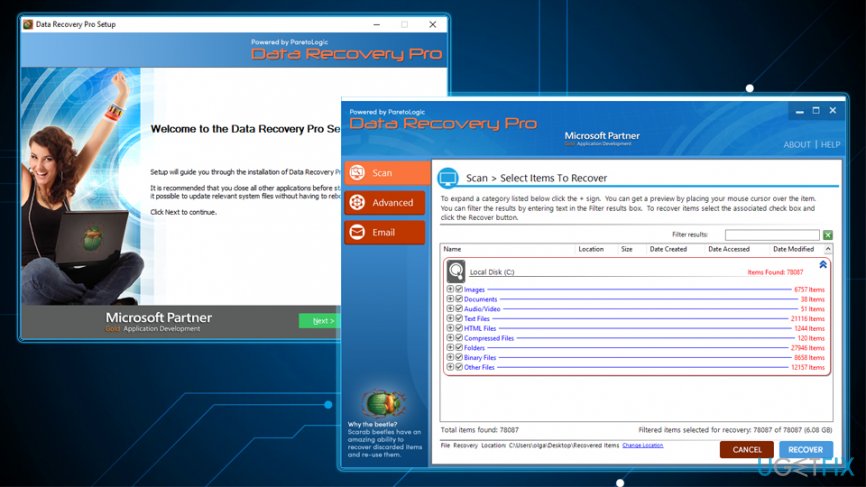
Data Recovery Pro was created to restore files that were accidentally deleted or lost after the system crash. However, the software can also help victims that need to recover data encrypted by Ryuk ransomware. Thus, it is worth a try:
- Download Data Recovery Pro and and follow on-screen instructions to install it on your device
- Open the application and set up a scan – pick Full Scan option and click on Start Scan
- You can also make the software look for specific files – simply enter a keyword
- As soon as the scan is complete, mark all the data you want to get back and press Recover
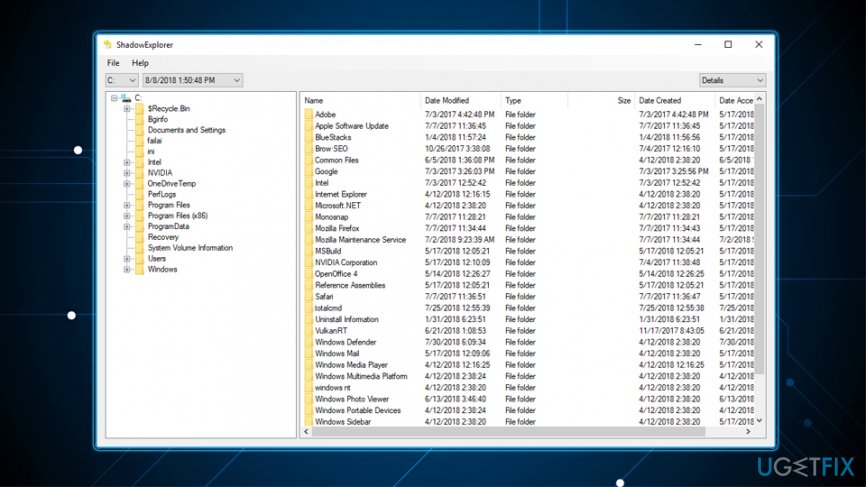
Retrieve files encrypted by Ryuk ransomware using ShadowExplorer
Most ransomware viruses target Shadow Volume Copies and delete them from Windows. However, this process might sometimes fail. In such case, ShadowExplorer will get all your data back:
- Download ShadowExplorer software and run the installation Wizard
- Open the app and select the drive you want to recover files from
- Click Export (you may also specify where to export files)
Resort to Windows Previous Version Feature to recover your files locked up by Ryuk virus
This method allows you to restore files one-by-one. Therefore, recovering a large amount of data might be impossible. Additionally, you should have System Restore function enabled before the malware infected your computer. If you meed these conditions, follow these steps to recover files encrypted by Ryuk ransomware:
- Select an encrypted file you want to restore and right-click it
- Choose Properties and then Previous Versions tab
- Pick a previous version and click Restore
Recover files and other system components automatically
To recover your files and other system components, you can use free guides by ugetfix.com experts. However, if you feel that you are not experienced enough to implement the whole recovery process yourself, we recommend using recovery solutions listed below. We have tested each of these programs and their effectiveness for you, so all you need to do is to let these tools do all the work.
Access geo-restricted video content with a VPN
Private Internet Access is a VPN that can prevent your Internet Service Provider, the government, and third-parties from tracking your online and allow you to stay completely anonymous. The software provides dedicated servers for torrenting and streaming, ensuring optimal performance and not slowing you down. You can also bypass geo-restrictions and view such services as Netflix, BBC, Disney+, and other popular streaming services without limitations, regardless of where you are.
Don’t pay ransomware authors – use alternative data recovery options
Malware attacks, particularly ransomware, are by far the biggest danger to your pictures, videos, work, or school files. Since cybercriminals use a robust encryption algorithm to lock data, it can no longer be used until a ransom in bitcoin is paid. Instead of paying hackers, you should first try to use alternative recovery methods that could help you to retrieve at least some portion of the lost data. Otherwise, you could also lose your money, along with the files. One of the best tools that could restore at least some of the encrypted files – Data Recovery Pro.
- ^ Lucia Danes. Organizations start facing the cruelty of Ryuk ransomware. 2-spyware. Malware insights and news.
- ^ Phishing. ACCC. Australian Completition & Consumer Commission.
- ^ Brute Force Attack. Technopedia. Technical information.
- ^ Volume Shadow Copy Service. Microsoft. Docs.



