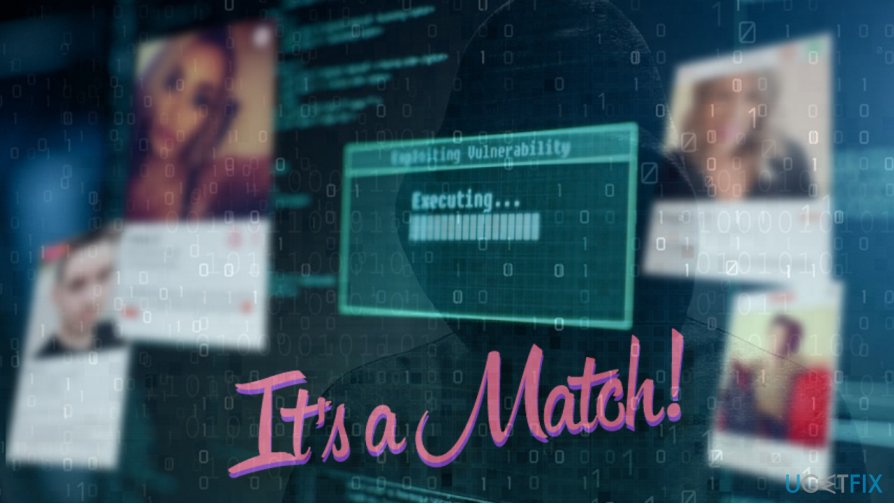
Hackers can leak swipes and private chats from Tinder accounts by only having victim's phone number
Tinder should take people's privacy more carefully. It's a second time[1] in this year when hackers manage to exploit Tinder's – one of the first swiping apps developed for dating – vulnerability and take full control over people's accounts.
The vulnerability has been detected by Appsecure[2] early last week and reported on February 20, 2018. Cybersecurity experts put all blame on Tinder that did not check user's account tokens generated by account kit against associated client IDs.
Tinder is related to Facebook as it relies on Facebook’s Account Kit[3] system to manage logins. The current attacked was executed by revealing two vulnerabilities – one in Tinder and the other in the mentioned Facebook’s Account Kit system. Hackers managed to gain access to account token and then took full control over Tinder accounts armed with just a phone number.
The culprit of the hack on Tinder's end, security experts say
Cybersecurity experts from Checkmarx claim that Tinder's vulnerability is the result of the ineffective use of encryption. In other words, the company does not do much to protect its clients the number of which has surpassed 20 billion.
The company is accused of not using HTTPS[4] protocols for encrypting profile pictures. Such security gap allows criminals to intercept traffic between the user's mobile device and their servers. Consequently, they can monitor user's profile picture and see what pictures he or she is reviewing.
Besides, it's quite easy for advanced IT specialists that hackers often are to find out the interaction of a particular person with a profile picture because Tinder's developers reveal that explicitly. Although the data is encrypted, the length of encoded text differs letting the attacker know how the user responded to a swipe.
However, the leakage of right left or up swipes is not the biggest problem. The latest Tinder's vulnerability allowed hackers to take over Tinder's accounts completely. By revealing the gap in Tinder's login system criminals get the access to people's profiles and chats, so having in mind that it's dating site that is supposed to ensure hundred percent protection, the consequences may be severe.
Amit Ashbel, one of the Checkmarx, perfectly illustrating the second Tinders exploit by comparing the overall Tinder's security politics to “someone standing over your shoulder looking at everything.”
People should be more careful with Wi-Fi hotspots
For the attack to take place, the potential victim and the attacker must be using the same Wi-Fi network or hotspot.[5] The criminals who exploited the vulnerability and knows the telephone number of a potential victim can then connect from his/her phone to Tinder and pull all the secrets from the dating service.
All photos, swipes, and matches that should be perfectly hidden from inquisitive are quite easily exploitable when sharing the same Wi-Fi network and using Tinder's iOS or Android app. Unencrypted profile pictures allow hackers to monitor every swipe left, swipe right, or match on the target's phone.
According to cybersecurity experts, Tinder should take immediate steps to patch both vulnerabilities. This can be done by moving to HTTPS and change the length of encryption texts of swipes to make them less visible. They also added that the same information leaking strategy does not limit to Tinder. Crooks might similarly exploit other social media platforms, so their developers should put more effort to protect people's privacy.
Leaking swipes on Tinder can induce ransomware developers
Experts speculate why someone would need to know which way one person swiped while viewing someone's profile picture. However, that's the point. Such information is valuable, especially in those cases of cheats, relationships outside marriage, same-sex relationship, and so on.
The attackers are targeting celebrities, and that's not surprising. They are most vulnerable to blackmailing and similar cyber crimes, so Tinder's vulnerability is yet another attempt to make fun and earn easy money.
- ^ Linas Kiguolis. Tinder vulnerability lets criminals spy on your swipes. 2-Spyware. Virus and Spyware news.
- ^ Anand Prakash. How I hacked Tinder accounts using Facebook’s Account Kit and earned $6,250 in bounties. Free Code Camp.
- ^ Fahmida Y. Rashid. Facebook Account Kit opens door to a world without passwords. InfoWorld. The leading voice in emerging enterprise technology.
- ^ Brian Jackson. What is the Difference Between HTTP and HTTPS?. KeyCDN. High-performance content delivery network (CDN).
- ^ Melanie Pinola. Mobile Work: What Is a Wi-Fi Hotspot?. Lifewire. Practical advice on how to live better with technology.



