Question
Issue: How to Uninstall .Wallet Ransomware?
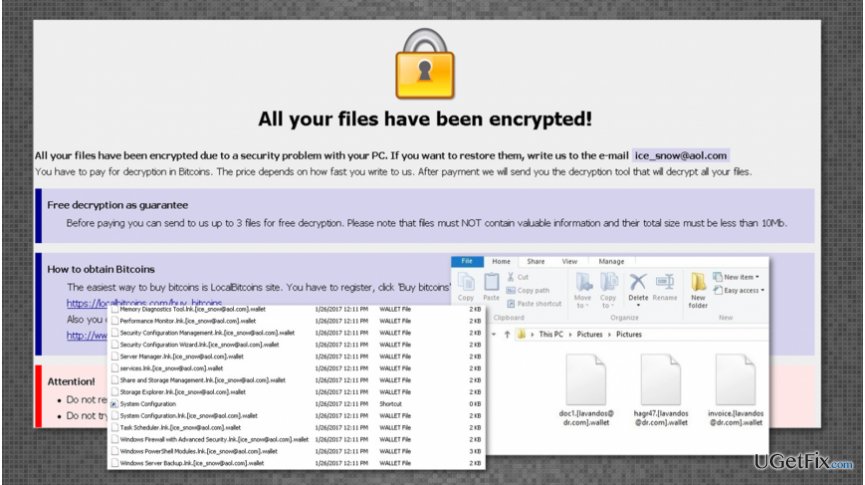
My all files have .wallet file extension, and a strange background picture asks to transfer 3 Bitcoins in order to decrypt my files. I have no idea why and when my computer was infected with ransomware. What do I need to do now?
Solved Answer
Wallet ransomware has two main distribution channels – malicious email attachments and malvertising. The first distribution method allows sending obfuscated Trojan in a misleading email which informs about a necessity to open an attached document. The second method allows placing malware-laden ads on any website. When a person clicks on the infected attachment or advertisement, the .wallet ransomware payload is installed on the system and activated.
Ransomware operation techniques
Previously discusses methods allows creators of the .wallet virus install and run a malicious payload on the system. Then, ransomware immediately starts scanning the system and encrypting targeted files. Using a sophisticated combination of RSA and AES algorithms, ransomware makes data inaccessible. Originally, encrypted files have .wallet file extension; however, other versions of malware might append different file extensions. However, all the details and name of the virus is presented in the ransom note which appears as a changed desktop wallpaper. The ransomware might also make entries in the Windows Registry in order to activate itself every time a person reboots an infected computer. These malicious processes require lots of CPU/RAM; as a result, the computer becomes slow and sluggish. Ransomware is also capable of opening the backdoor for potentially unwanted programs (PUPs) and malware.
How to uninstall .wallet ransomware?
Before starting .wallet removal procedure, we highly recommend reading the instructions carefully first. Also, you should print them because elimination requires restarting the computer and closing the browser.
1. Reboot your computer to the Safe Mode with Networking.
2. When in Safe Mode, open Windows Task Manager by clicking Ctrl + Shift + Esc at the same time.
3. Go to the Processes Tab. Find malicious processes in the list. Right-click on them and choose Open File Location.
4. Once the folder is opened, end malicious processes and delete their folders.
5. Hold the Start Key and R, paste the following command and click OK:
notepad %windir%/system32/Drivers/etc/hosts
This will open a new file where you will find a list of IP addresses that are connected to the computer.
6. In the search field type msconfig and press enter. This will initiate System Configuration window.
7. In the System Configuration Window go to Startup Tab. Deselect all Startup Items that have Manufacturer titled as “Unknown.” However, sometimes malware include fake names of the Manufacturer. Thus, you need to make sure which processes are dangerous and which ones are real.
8. Open Windows Registry by typing Regedit in the search bar and pressing Enter.
NOTE. Making modifications in Registry may lead to irreparable damage. Thus, in order to avoid possible damage, we recommend employing malware removal tools such as Reimage, and eliminating .wallet ransomware automatically.
9. When Windows Registry opens up, press CTRL + F and type the virus name. Look for the ransomware in the registry entries and delete them. Make sure you delete malicious files, not the legitimate ones.
10. In the Windows Search Field type these entries:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Check if something was added to these directories recently, and delete all entries from Temp.
Data Recovery options
Authors of the file-encrypting virus offers to purchase Wallet decryptor for particular amount of Bitcoins (different versions of the virus might ask for the different size of the ransom). However, cyber security experts does not recommend making this purchase, and focusing on virus removal. The main problem with the ransomware viruses is that deletion of the virus does not recover encrypted files. In order to recover files encrypted by .wallet ransomware, you can try to use Dharma decryptor. This crypto-malware belongs to the same ransomware family. Thus, this decryption tool should help to get back access to the files.
Get rid of programs with only one click
You can uninstall this program with the help of the step-by-step guide presented to you by ugetfix.com experts. To save your time, we have also selected tools that will help you carry out this task automatically. If you are in a hurry or if you feel that you are not experienced enough to uninstall the program by your own, feel free to use these solutions:
Access geo-restricted video content with a VPN
Private Internet Access is a VPN that can prevent your Internet Service Provider, the government, and third-parties from tracking your online and allow you to stay completely anonymous. The software provides dedicated servers for torrenting and streaming, ensuring optimal performance and not slowing you down. You can also bypass geo-restrictions and view such services as Netflix, BBC, Disney+, and other popular streaming services without limitations, regardless of where you are.
Don’t pay ransomware authors – use alternative data recovery options
Malware attacks, particularly ransomware, are by far the biggest danger to your pictures, videos, work, or school files. Since cybercriminals use a robust encryption algorithm to lock data, it can no longer be used until a ransom in bitcoin is paid. Instead of paying hackers, you should first try to use alternative recovery methods that could help you to retrieve at least some portion of the lost data. Otherwise, you could also lose your money, along with the files. One of the best tools that could restore at least some of the encrypted files – Data Recovery Pro.



