WannaCry ransomware has caused excessive damage to home users, businesses and organizations alike. The virus encrypted millions of user files with strong AES and RSA encryption algorithms, rendering them inaccessible and virtually useless.
Though the main wave of the attack has quieted down rather quickly, the outcomes of this incident still continue. Users keep reporting that extensions of their files have been appended with unfamiliar .wcry, .wncryt or .wncry endings. Besides, every WCry attack also involves dropping copies of the file called @[email protected] on every infected folder. This document includes the extortionists’ vision of data recovery. In particular, the criminals demand the victims to send money for the personalized data recovery key, claiming that it is the only chance they have to ever get the access to their files back.
The victims have started panicking when two weeks after its appearance the virus code was still a mystery to the experts. The few choices that they had were either to remove the virus but lose their files or to take a major risk and collaborate with the cybercriminals by paying the ransom.
Let’s be fair here: not everyone can wave off $300 to $600 USD that easily, so most WannaCry victims choose to lose their valuable documents instead. Luckily, a software released by Benjamin Delpy (@gentilkiwi) on Github gives hope that not everything is lost yet.
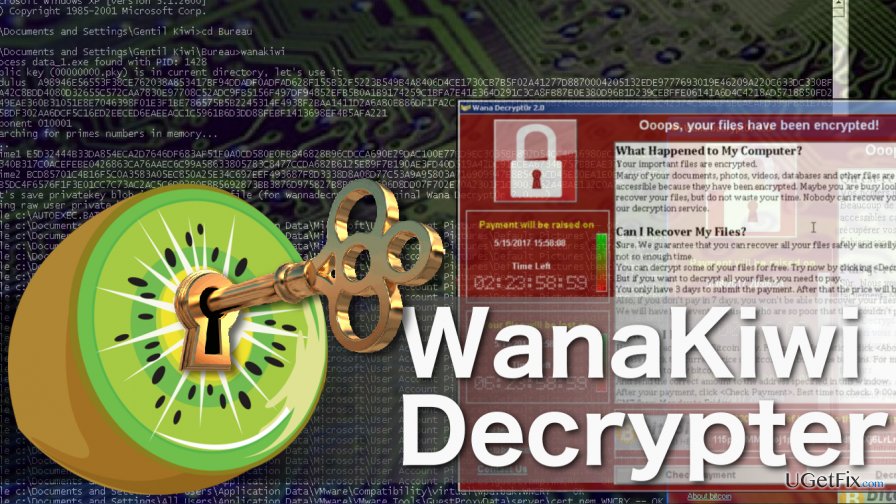
A software called Wanakiwi may be the solution the ransomware victims have been waiting for. This tool works on most infected Windows operating systems, including Windows XP, Windows 7, Windows Vista and others.
The working principle of this software is simple: Wanakiwi tries to recover the decryption key from memory by finding prime numbers. If these numbers change — the tool will become useless. Thus, the data recovery can only be carried out if the computer has not been rebooted yet.
Besides, to prevent further data encryption, the decrypter also recovers .dky files which prevent WannaCry’s encryption functionality. We have prepared more detailed instructions on how to prepare for the data recovery and how to use Wanakiwi below:
- The first thing you want to do before obtaining Wanakiwi decrypter is backup the encrypted files so you would be able to recover them in the case of an emergency. The backup will be useful in case files get accidentally damaged during the recovery procedure, though it is very unlikely to happen. Use software like CryptoSearch to speed up the backup procedure.
- The second step — download the Wanakiwi decryptor! Make sure you obtain the program from a reputable source — the creator’s official page.
- Wanakiwi is an easy-to-use decrypter which only requires you to launch it. The rest of the key recovery and decryption of data will be carried out manually. A little patience and you will soon be able to enjoy the access to your personal files again.
- Finally, when your data is decrypted, you must delete the virus along with its malicious components from your computer. Do it immediately after the data recovery process is complete. Run a scan of your computer with Reimage or similar professional security utility.



